The AI That Broke the Grid: Solving Erdős’s Unit Distance Problem
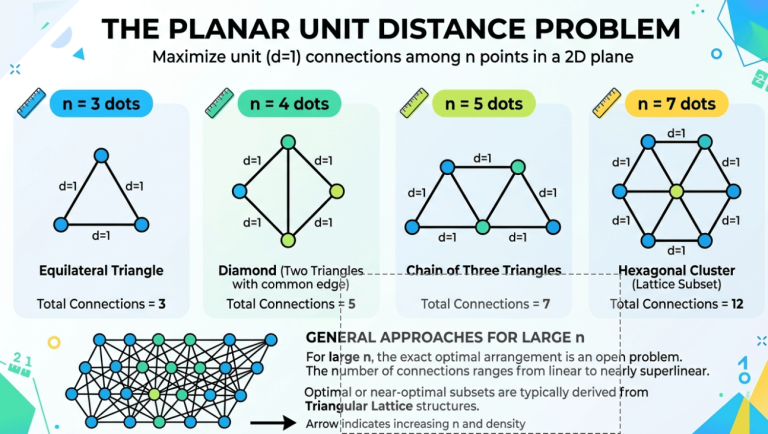
Imagine you are standing in an infinitely large, perfectly flat room. I hand you a bucket of marbles and a simple set of rules: place marbles on the floor. Your goal is to arrange these marbles so that as many pairs as possible are exactly one meter apart from each other. If I give you …